A Quick Understanding of Owasp top 10
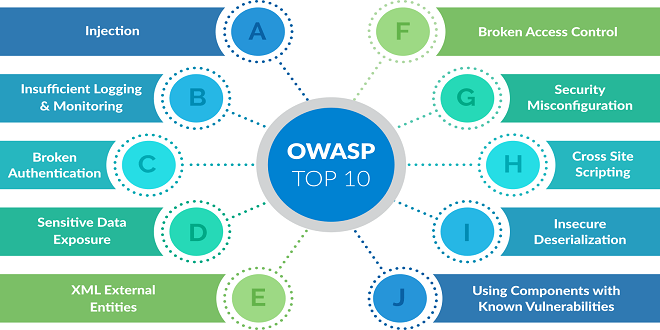
This is an Open Web Application Security Project that upkeeps a regularly-updated list of the most persistent web application security apprehensions. Actually, this The Open Web Application Security Project, or OWASP, is actually an international non-profit organization. It is devoted to web application security. One of OWASP’s main principles is that all of their stuff gets freely available and conveniently accessible on their website, making it possible for anybody to enhance their own web application security.
The OWASP Top 10 is a frequently-updated report. It outlines security concerns for the security of web application. It concentrates on the ten most crucial risks. The report is put together by an expert team of security professionals from all over the world. Actually, this OWASP refers to the top ten as an that of awareness document and they endorse that all companies and businesses incorporate the report into their procedures so as to minimize or ease security risks. Here are a few of the security risks reported for your understanding.
Broken Authentication
Susceptibilities in authentication (login) systems may give attackers access to user accounts and even the capability to compromise a whole system using an admin account. For example, an attacker may take a catalogue containing thousands of known usernames or that of password combinations obtained during any data breach and use a script to simply try all such combinations on a login system to find out if there are any sort of work. A few of the strategies that you can use to alleviate authentication vulnerabilities are needing two-factor authentication (2FA) and restricting or delaying recurrent login attempts using rate limiting.
Injection
Injection attacks take place once untrusted data gets sent to a code interpreter via a form input or that of some other data submission to any web application. For example, an attacker might enter SQL database code into a form that supposes a plaintext username. In case that form input is not rightly secured, this might end up in that SQL code getting executed. This is called SQL injection attack.
Remember that you can ensure that these Injection attacks are prevented by validating or simply sanitizing user-submitted information. Here, Validation simply means rejecting suspicious-looking data. Whereas, sanitization refers to cleaning up the suspicious-looking portions of the data.) Other than this, a database admin may set controls to minimalize the sum of information an injection attack may expose.
Sensitive Data Exposure
In case web applications do not really protect sensitive data like that of financial information and passwords, attackers may get access to that data and seller make use it for wicked purposes. One well-known method for stealing sensitive information is making use of an on-path attack.
Data exposure risk may get minimized by encrypting all sort of sensitive data and also disabling the caching* of any sort of sensitive information. Other than this, web application developers must also take care to promise that they are not gratuitously storing any sensitive data.
Here, you should know that caching is the practice wherein data gets stored temporary for re-use. For example, web browsers are often keeping cache webpages so that in case a user revisits the web pages within a fixed period span, the browser does not need to get the pages from the web.
Broken Access Control
Access control is all about a system that actually controls access to information as well as functionality. Broken access controls permit attackers to avoid authorization and perform tasks as though they actually were advantaged users like that of administrators. For example, a web application might permit a user to alter which account they are signed in as simply by altering part of a URL, in the absence of any other sort of verification.
Well, these access controls may be secured by ensuring that a web application makes use of authorization tokens* and sets strict controls on them. You know various services issue authorization tokens once users log in. Every privileged request that any user makes is going to ask for that the authorization token get present. This is a safe way to make sure that the user is who they say they actually are, without need to constantly enter their sign in credentials.
Security Misconfiguration
It is the most common susceptibility on the list, and it is even often the outcome of using default configurations or displaying disproportionately verbose errors. For instance, one application might display a user overly-descriptive errors that could reveal vulnerabilities in the application. You can ensure that such a thing gets mitigated by eradicating any unused features in the code and promising that error messages are better general.
. Cross-Site Scripting
Cross-site scripting susceptibilities occur once web applications allow users to add custom type of code into a URL path or that of onto a website that is going to be seen by other users. This vulnerability may be exploited to run spiteful JavaScript code on the browser of a victim. For example, an attacker might actually send an email to a victim that looks like to be from a trusted bank, with a link to the website of that bank. Such a link could have some malicious type of JavaScript code tagged onto the end of the URL. In case the bank site is not actually protected against cross-site scripting, then such a malicious code is going to be run in the web browser of the victim once he or she clicks or taps on the link.
Mitigation plans for cross-site scripting encompassing escaping untrusted HTTP requests and validating or simply sanitizing user-generated content. Using modern type of web development frameworks like reacts and Ruby on Rails even provides some built-in cross-site scripting defines.
Use of Components With Known Vulnerabilities
Various modern day web developers use components like libraries and frameworks in the overall web applications. Such are ethe components that are parts of software that aid the developers avoid redundant work and offer needed functionality; common example encompasses front-end frameworks such as React and tinier libraries that used to add share icons or even that of a/b type of testing. A few of the attackers even look for vulnerabilities in such components that they can then use to score attacks.
Conclusion
To sum up, you can check out guidance from professional experts at Appsealing and ensure that you get the solutions for your vulnerabilities.